THE TECHNICAL ADVANTAGES OF ANY PROPOSED SOLUTIONS TO THE CUSTOMER
Any proposed solutions for any customer will be robust, centralized, narrow bandwidth consideration; multi-tier, schema-based, so that all the modules, features, sub-modules, and functionality will be under a single umbrella. Based on the centralized solutions, it will help as follows:
- Multi-tier service the architecture will ensure all the service levels in a small schema and ensure module, sub-module, and feature-wise service to the entire user level.
- More than 10,000 concurrent users can access the system at a time.
- Because any proposed system for the customer will be designed for narrow bandwidth, a minimum of 4 kilo bandwidth will be sufficient to access the system.
- Any report with up to 6 million records in data can be generated in 3 seconds.
- The system will be flexible enough to handle 20–35% user growth per year in any proposed system.
- For any feature, page login and response, service request and response time is within seconds.
- The proposed system will be designed in such a way that it can be up-to-date for the next decade (at least 10 years) due to updated tools and technology.
- The proposed system will be designed by considering 2G to 5G network accessibility and user-friendliness.
- The proposed system will be designed with an API-based system so that at any time, the customer can integrate any system with the proposed system without a major change in architecture level.
- The system will be designed with PWA (Progressive Web App) so that without the Internet, the users (Service Providers and Recipients) will access limited information for the application.
- The proposed system will ensure manual and automated testing so that system acceptance and functionality will be robust and smooth with almost zero errors.
- The proposed system will ensure guidance to users for data input (Type, Sample) as a popup system and notification in the respective input field.
- The proposed system will ensure web application compatibility for all browsers and devices (Standard), allowing users to use the Web, Android, Tablet, and iOS devices. (RESPONSIVE)
- All mobile applications (iOS and Android) must use the API for data mapping so that security issues will not be a threat.
TECHNOLOGIES WE USE
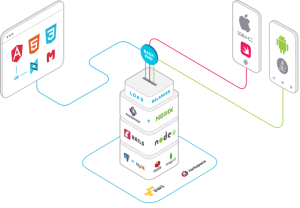
| Microsoft | Java | JavaScript | PHP | ||||
| ASP.net Web Form | Spring.io | MVC/MVVM Framework | Laravel | ||||
| ASP.net Web API/MVC 4 | Struts | Angular.js | CodeIgniter | ||||
| SharePoint 2013/2010 | Hibernate | Node.js | CakePHP | ||||
| Signair | Maven | Express.js | Yii | ||||
| C# | Axis 2 | Jade | Symphony | ||||
| JSTL | jQuery | ||||||
| Mobile Platform | Database | Server & Cloud | Mise | ||||
| Android | SQL Server | Weblogic | SAS | ||||
| Windows Phone | MongoDB | Nginx | Bootstrap | ||||
| Phonegap | MySQL | Sun One | Socket IO | ||||
| Xamarin | RavenDB | AWS | Glup & NPM | ||||
| Vuforia | Oracle | Azure | Bower | ||||
| Unity 3D | Rackspace | Python | |||||
| iOS (Native) | |||||||
DEVELOPMENT PROCESS AND IMPLEMENTATION
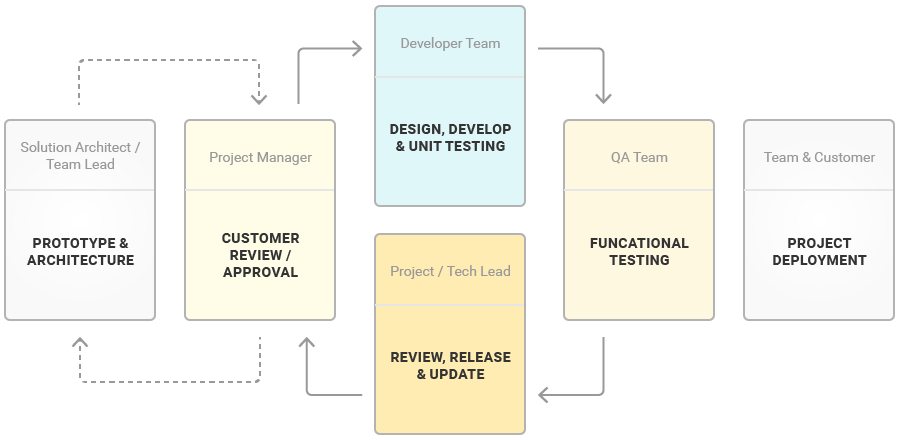
Fawz Biz Enterprises has a proven approach to project management that results in timely and successful software installation and implementation. We conduct a special planning process for each new project to ensure that both the customer and their requirements are the primary focus of all personnel assigned to the project.
We also ensure that any unique or customized improvements to standard product offerings are well understood by all participants.
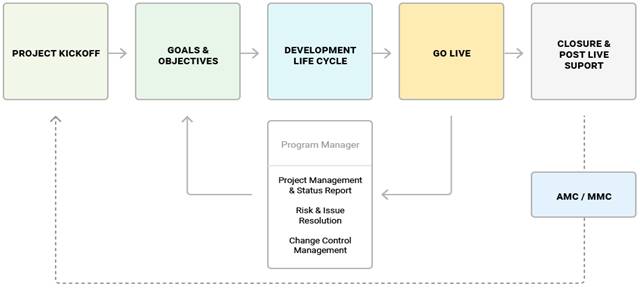
Our implementation is a stepped activity, with the customer playing a significant role in ensuring success at every milestone. To ensure the smooth progress of all work done, a number of tasks have to be performed individually or jointly.
PROJECT GOVERNANCE & MANAGEMENT
Project governance is a consistent and structured approach to delivering projects, utilizing a standard set of principles and policies to manage change, process, people, and resources.
The program’s governance framework will provide appropriate controls and escalation paths for the management and resolution of issues, approval of changes in program directions, program scope, and benefits management.
| Meeting Type | Owner | Frequency | Participants | Outcome |
| Action Tracking Meeting | Project Manager | Weekly | Project Manager, Technical Manager, Technical Leads | Detailed Action Tracker |
| Project Review Meeting | Tech Lead | Fortnightly | Project Director, Technical Director, Project Manager(s), Technical Manager(s) | Project Status Report Updated Project Plan |
| Project Governance Meeting | Global Project Delivery Head | Bi-Monthly | GPD Head, Project Engineering Head, Project Director, Technical Director | Project Governance Report |
| Project Sponsors Meeting | CTO | Monthly | CTO, Project Director | MoM & Future Strategy for the product |
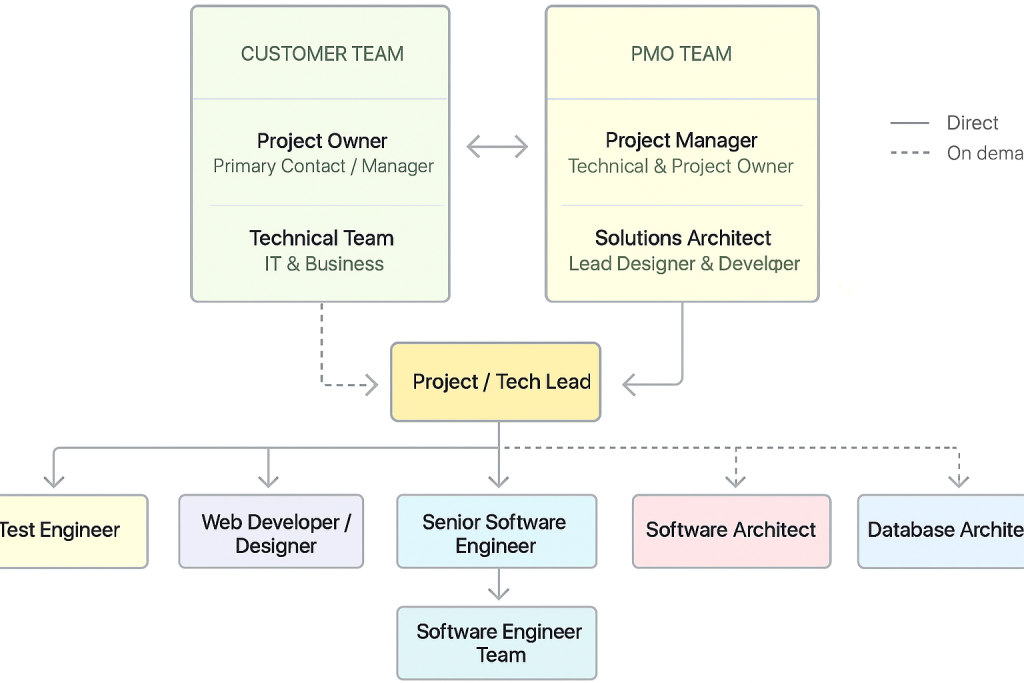
TEAM ENGAGEMENT MODEL
FAWZ Biz Enterprises has a well-defined program organization structure that enables smooth, zero-defect, and on-time project deliveries. The program and project organization structure will ensure the effective use of resources and provide proper coordination among the various interfaces. An organization functions best when the members know their role and understand their responsibilities.
RISK CONTROL
Risk management involves all activities pertaining to the identification, analyzing, and making provision for predictable and non-predictable risks in the project. Following are the steps of risk management in FAWZ Biz Enterprises –
| Identification – Making a note of all possible risks that may occur in the project. |
| Categorize – Categorizing known risks into high, medium and low risk intensities as per their possible impact on the project. |
| Manage- Analyzing the probability of the occurrence of risks at various phases. Making a plan to avoid or face risks. Attempting to minimize their side-effects. |
| Monitor- Keeping a close eye on potential risks and their early symptoms. Also monitoring the effects of steps taken to mitigate or avoid them. |
CHANGE CONTROL PROCESS
Change Control is the process of handling proposed alterations to items that have been previously designated as fixed. This means that an item only becomes subject to change control once it has been signed-off, stored in a baseline and placed under configuration control.
![]() Definition of Change Control
Definition of Change Control
Change Control is concerned with –
- Assessment of the impact of potential scope changes
- Putting potential scope changes in order
- Choosing a course of action in response to potential changes
![]() Aim of Change Control
Aim of Change Control
The aim of change control is to ensure that if a signed-off item is changed, then –
- All stakeholders have an opportunity to participate in the control of any subsequent changes.
- There is will be an audit trail which connects a change to a configuration item to the reason for its change, and which will records the participation and authorization of those people concerned with the change.
- All recipients will be made aware of any changes that may occur.
![]() Change Control Guiding Principles
Change Control Guiding Principles
Certain principles will guide the use and implementation of the Project Change Control process. The principles include:
- The Change Control process is intended to facilitate the timely analysis and decision-making of change requests.
- Individuals initiating requests will use the Business Requirement Document (BRD) Form to articulate
how the change helps the business meet its overall objectives and quantify the benefits gained by the business due to the change.
- An impact assessment will be performed by the project team to assess the impact of potential changes.
- The Change Control Authority has full authority to make approval decisions.
Requests for scope changes will be considered if, and only if, the Project Change Request process is followed.
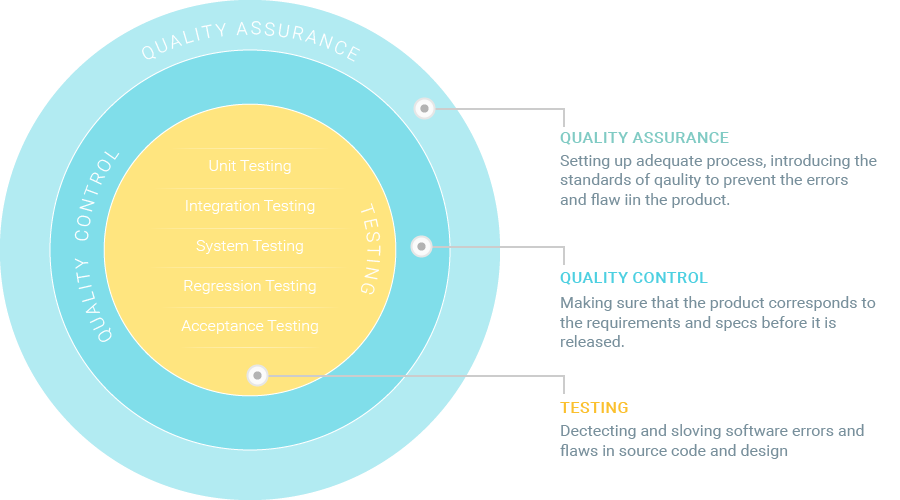
SOFTWARE QUALITY MANAGEMENT
The structural quality of the software is usually hard to manage: It relies mostly on the expertise of the engineering team and can be assured through code review, analysis, and refactoring.
At the same time, functional aspects can be assured through a set of dedicated quality management activities, which include quality assurance, quality control, and testing.
SOFTWARE TESTING
Typically, the testing covers the following levels of the software:
Unit Testing
The smallest testable part of the software system is often referred to as a unit. Therefore, this testing level is aimed at examining every single unit of a software system in order to make sure that it meets the original requirements and functions as expected.
Unit testing is commonly performed early in the development process by the engineers themselves, not the testing team.
Tools & Method: Automated, Junit, Test NG, PHP Unit
Integration Testing
The objective of the next testing level is to verify whether the combined units work well together as a group. Integration testing is aimed at detecting flaws in the interactions between the units within a module. There are two main approaches to this testing: bottom-up and top-down methods.
Bottom-up integration testing starts with unit tests, successively increasing the complexity of the software modules under test.
The top-down method takes the opposite approach, focusing on high-level combinations first and examining the simple ones later.
Tools and Methods: Automated, Soap UI, Rest Client
System Testing
At this level, a complete software system is tested as a whole. This stage serves to verify the product’s compliance with the functional and technical requirements and overall quality standards.
System testing is performed by a highly professional testing team in an environment as close to the real business use scenario as possible.
Tools and Methods: Automated (Webdrive) Exploratory Testing
Regression Testing
Regression testing is aimed at identifying code incompatibilities by testing existing software applications to ensure that changes or additions haven’t broken any existing functionality.
The major benefits of automated regression testing are that testing scenarios can be re-run over and over again without any hassle to ensure that the new changes made did not result into a regression, or caused previously functional components to fail.
Tools & Methods: Automated, TestDrive
Load and Performance Testing
The definitive advantages of automated testing in this case are the multiple load and performance tests you can run simultaneously on different devices. It is possible to emulate as many users as possible to ensure the final product is absolutely stable and can handle high traffic.
Acceptance Testing
This is the last stage of the testing process, where the product is validated against the end user requirements and for accuracy. This final step helps the team decide if the product is ready to be shipped or not. While small issues should be detected and resolved earlier in the process, this testing level focuses on overall system quality, from content and UI to performance issues.
The acceptance stage might be followed by alpha and beta testing, allowing a small number of actual users to try out the software before it is officially released.
Tools and Methods: Automated, Cucumber
SECURITY CONSIDERATION
While a system may always have implementation defects, or “bugs,” we have found that the security of many systems is breached due to design flaws, or “flaws.” We believe that if we can design a secure system that avoids such flaws, it can significantly reduce the number and impact of security breaches. While bugs and flaws are both different types of defects, we believe there has been quite a bit more focus on common bug types than there has been on secure design and the avoidance of flaws.
At Fawz Biz Enterprises, the focus is to build a flawless system that takes security best practices (i.e., the “Top 10 Most Critical Web Application Security Risks” by OWASP) into consideration at every level of design, development, and implementation. The following are the core security procedures maintained during development.
![]() Authentication Mechanism & Authorization
Authentication Mechanism & Authorization
Once a user has been authenticated, a securely designed system should also prevent that user from changing their identity without re-authentication.
- A multi-factor (sometimes referred to as an N-factor) authentication technique requires multiple distinct factors to prove a user’s identity.
- Security control mechanism to ensure that the user’s access rights to the data are limited to only his/her authorized access level.
- Access to resources is granted with the least privilege to ensure that accounts have the least amount of privilege required to perform their job functions and be responsible. This encompasses user rights and resource permissions, including file and database permissions.
![]() Data Validation
Data Validation
- Design or use centralized validation mechanisms to ensure that all data entering a system (from the outside) or major component (from another component of the same system) is appropriately validated.
- Transform data into a canonical form, before performing actual syntactic or semantic validation. This ensures that validation cannot be bypassed by supplying inputs that are encoded in a transport encoding, or in a possibly invalid non-canonical form.
- Use common libraries of validation primitives, such as predicates that recognize well-formed email addresses, URLs, and so forth.
- Explicitly re-validate assumptions about “nearby” code that relies on them.
- Use implementation-language-level types to capture assumptions about data validity.
![]() Cryptography
Cryptography
Cryptography is one of the most important tools for building secure systems. Through the proper use of cryptography, it is possible to ensure the confidentiality of data, protect data from unauthorized modification, and authenticate the source of data. Cryptography can also enable many other security goals as well.
- Authentication: Using a cryptographic system, we can establish the identity of a remote user (or system). A typical example is the SSL certificate of a web server, providing proof to the user that he or she is connected to the correct server.
- Non-Repudiation: It is particularly important for financial or e-commerce applications. Often, cryptographic tools are required to prove that a unique user has made a transaction request. It must not be possible for the user to refute his or her actions.
- Confidentiality: More commonly, the biggest concern is keeping information private. Whether it is passwords sent during a log on process, or storing confidential medical records in a database, encryption can assure that only users who have access to the appropriate key will get access to the data.
- Integrity: We can use cryptography to provide a means to ensure data is not viewed or altered during storage or transmission. Cryptographic hashes, for example, can safeguard data by providing a secure checksum.
![]() Identifying & Handling Sensitive Data
Identifying & Handling Sensitive Data
Data is critical to organizations and to users. One of the most important tasks that systems designers do is identify sensitive data and determine how to protect it appropriately.
- As data sensibility depends on many factors, including regulation, company policy, construction obligation, and users’ expectations, a policy is designed by the system engineers at the very beginning of the development phase to explicitly identify different levels of classification. Data Sensibility Policy factors all relevant considerations into the design.
- Technical data sensitivity controls that a designer might consider include access control mechanisms (including file protection mechanisms, memory protection mechanisms, and database protection mechanisms), cryptography to preserve data confidentiality or integrity, and redundancy and backups to preserve data availability.
- Data sets transit between components within a single system and between organizations. As data sets transit between systems, they may cross multiple trust boundaries. Identifying these boundaries and rectifying them with data protection policies is an essential design activity.
- Regular revisiting and revising of data protection policies and their design implications as policy requirements and data sensitivity can change over time.
![]() Analyzing Security Impact of External Component Integration
Analyzing Security Impact of External Component Integration
![]() Considering Future Changes to Objects & Actors
Considering Future Changes to Objects & Actors
![]() Audit Log
Audit Log
![]() OWASP Web Application Security Checklist
OWASP Web Application Security Checklist
The OWASP Top 10 is a powerful awareness document for web application security. It represents a broad consensus about the most critical security risks to web applications. During development, this checklist is considered carefully.
- Injection prevention
- Broken Authentication and Session Management
- Cross-Site Scripting (XSS)
- Broken Access Control
- Security Misconfiguration
- Sensitive Data Exposure
- Insufficient Attack Protection
- Cross-Site Request Forgery (CSRF)
- Using Components with Known Vulnerabilities
- Under protected APIs
![]() Back-up & Recovery
Back-up & Recovery
- Synchronized replication of data wherever applicable and upon agreement
- Point-in-time-recovery (PITR)
- Nightly full back
TRAINING & DOCUMENTATION MANAGEMENT

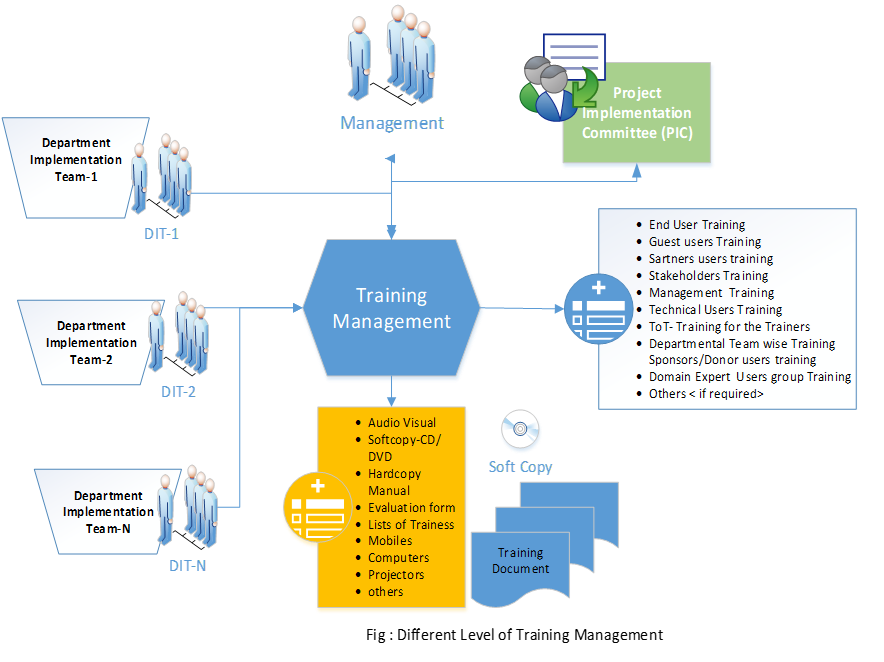
Training Type:
- Functional/ Business
- Technical( Admin, infra)
- End users
Major Software Product/Services
The Following Software Programs Were Planned and Developed by Fawz Biz Enterprises:
- Financial Accounting Software
- Software for Inventory Management
- Human Resource & Payroll System
- Business ERP
- AR/VR & Gamification Solutions
- Municipality Management System Software
- Healthcare Management System (with M2Sys CloudApper)
- National ID & eID Solutions (AFIS/ABIS, with M2Sys CloudApper)
- Biometric Voter Registration (with M2Sys CloudApper)
- ePolice™ – Law Enforcement & Case Management (with M2Sys CloudApper)

